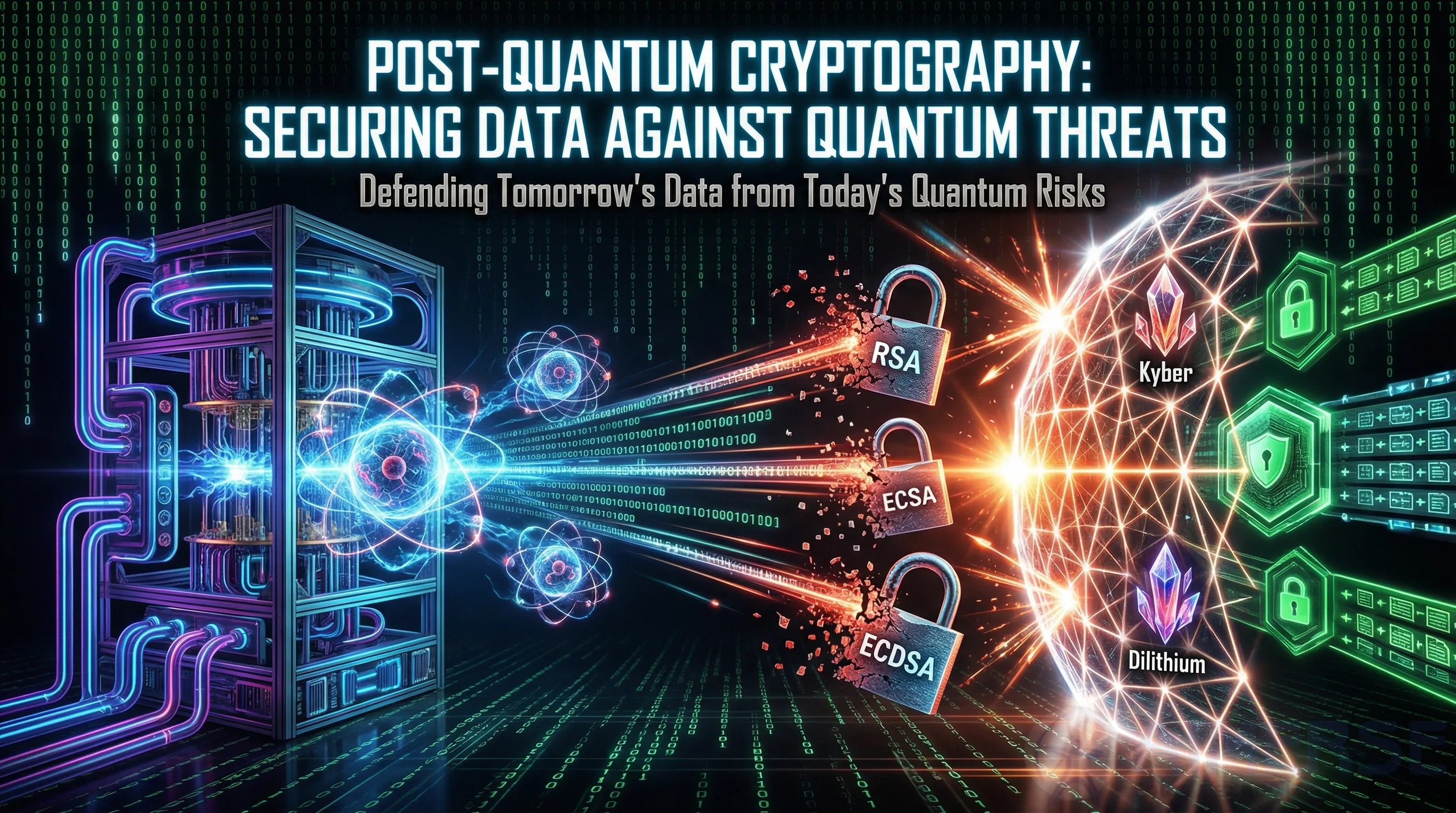
Post-Quantum Cryptography: Securing Data Against Quantum Threats
Post-quantum cryptography (PQC) is the armor we require against quantum-capable attackers, such as Shor’s algorithm, particularly for data in transit and at rest in 2026.
With the advent of quantum computers with more than a million qubits (circa 2026-2030), they could potentially break RSA and ECDSA using Shor’s algorithm, rendering today’s encrypted communications vulnerable to decryption at a later date—the “harvest now, decrypt later” problem. The NIST-selected PQC schemes—Kyber for key encapsulation, Dilithium for signatures, and Falcon—use lattice cryptography, hash functions, and error-correcting codes to provide 128-bit+ security. To facilitate a smooth transition, hybrid schemes that mix classical and PQC cryptography have been developed with less than 10% overhead.
Core PQC schemes
- Lattice-based (Kyber/Dilithium): Based on the hardness of problems such as the shortest vector problem in lattices; enables fast and secure key exchange.
- Hash-based (SPHINCS+): Based on collision resistance; provides stateless signatures.
- Code-based (Classic McEliece): Based on decoding linear codes; provides exceptionally high security but with larger key sizes.
These can be combined using OpenQuantumSafe libraries with Node.js TLS or Spring Boot.
What needs to be done by enterprises
- TLS upgrade: Introduce PQC in the handshake procedure for web applications (React front-ends, for example).
- VPN and key management: Secure data repositories in Django, Laravel, and other frameworks.
- Blockchain: Employ quantum-resistant signatures for transactions.
Trade-offs and testing
Key sizes can increase to 1-10 KB, which might affect bandwidth. Testing and validation with PQCRYPTO tooling.
Migration plan
- Crypto usage audit (scan Spring Boot dependencies, for example).
- Hybrid scheme prototyping with libraries like liboqs.
- Crypto-agile API deployment in Node.js.
- NIST FIPS 203/204 certification of implementations.
By 2026, browser support will increase in Chrome and similar technology stacks.
Conclusion
Once PQC goes mainstream, it is essential to fortify the stack from front-end to back-end: React.js for client security, Node.js for agile protocols, Python Django for encrypted business logic, Laravel for rapid hardening, and Java Spring Boot for enterprise compliance.